Cisco ASA AnyConnect vpn configuration with radius authentication and dynamic acl
In this blog post, we will configure Cisco ASA firewall for AnyConnect VPN. Remote users will be authenticated against a radius server to get access to the VPN and traffic filtering/firewalling will be done using downloadable dynamic acl from the radius server.
Here we are using the exact same concepts from our previous blog post, just introducing radius authentication and downloadable acl from radius server.
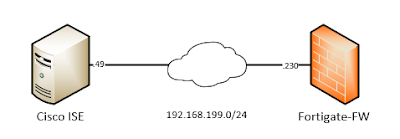
Let's as usual introduce our topology -
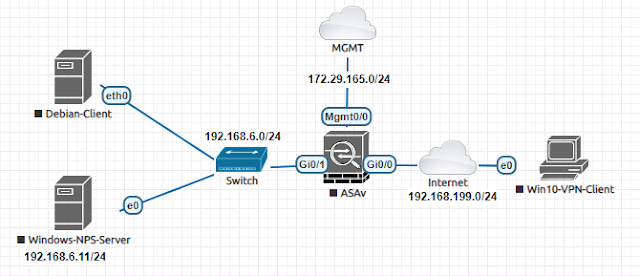 |
| 01 - AnyConnect VPN Topology |
The topology is straight forward. We have a inside network (192.168.6.0/24). Outside network is 192.168.199.0/24 where the ASA listens for anyconnect connections. And a management network 172.29.165.0/24 which is just a out-of-band management network for ASA.
We have a Win10-VPN-Client which will try to connect to inside network through anyconnect vpn. Debian-Client is just a client device in inside network to verify vpn connectivity. And Windows-NPS-Server is a radius server running NPS service. This NPS server is responsible for authenticating vpn users. And after successful authentication, the NPS server also sends a access control list, which the ASA receives and assigns to the vpn user.
Basic network connectivity configuration
Let's look at our interface and it's related IP configuration -
# show running-config interface
!
interface GigabitEthernet0/0
nameif outside
security-level 0
ip address dhcp setroute
!
interface GigabitEthernet0/1
nameif inside
security-level 100
ip address 192.168.6.1 255.255.255.0
!
interface Management0/0
no management-only
nameif mgmt
security-level 0
ip address dhcp
AnyConnect VPN configuration
We will activate a feature in the ASA so that our vpn traffic is not subjected to ASA's firewall inspection. Our vpn traffic will not be inspected by asa firewall. Instead it will be inspected by a vpn filter in ASA. Experienced ASA administrators knows about this feature; otherwise the readers can google about it to know more details.
!!! VPN traffic bypasses ASA firewall, instead will be inspected by a vpn filter
(config)# sysopt connection permit-vpn
We will use a redirect from http to https so that VPN users see our anyconnect web page only in https.
(config)# http redirect outside 80
We will use strong security protocol suites on our vpn connection. We will only accept tlsv1.2 or dtlsv1.2 and use higher encryption cipher suite. This step is optional; but highly recommended.
!!! Activating only most secured options for creating tunnel over https/ssl protocol
ssl client-version tlsv1.2
ssl server-version tlsv1.2 dtlsv1.2
ssl cipher dtlsv1.2 high
ssl cipher tlsv1.2 high
As our authentication and traffic filtering (downloadable dynamic acl) will be done by radius/nps server, we will define those first -
!!! Define a radius server group
aaa-server anyvpn-radius-server-group protocol radius
!!! Add the actual server to our defined group
aaa-server anyvpn-radius-server-group (inside) host 192.168.6.11
key test123
authentication-port 1812
accounting-port 1813
Then we will enable anyconnect vpn on the outside interface -
webvpn
!!! Users can download anyconnect client package, when they connect to VPN web page.
anyconnect image disk0:/anyconnect-win-4.9.01095-webdeploy-k9.pkg
!!! Outside interface will listen for anyconnect connection
enable outside
!!! Finally we enable anyconnect
anyconnect enable
!!! Optional command, when we want to allow users to select a user group alias when logging through web browser.
tunnel-group-list enable
We need an IP pool from where our successful authenticated users will be assigned an IP adress.
!!! Anyconnect users will get an IP adress from the pool below
ip local pool anyvpn-pool 192.168.7.101-192.168.7.200 mask 255.255.255.0
We will use split tunneling for our vpn. Only required networks will be tunneled through the VPN. For example, a remote user internet access will be done still through his local ISP, will not be routed through the VPN. In our case, we will only tunnel network traffic to our inside network (192.168.6.0/24).
!!! Only traffic to 192.168.6.0/24 is routed through the VPN
access-list split-networks standard permit 192.168.6.0 255.255.255.0
Now we will define a group policy for the vpn -
group-policy anyvpn-radius-group-policy internal
group-policy anyvpn-radius-group-policy attributes
!!! We will just activate vpn with anyconnect client. Client-less access through web browser is not allowed.
vpn-tunnel-protocol ssl-client
!!! We are doing split tunneling, only networks defined by split-networks will be tunneled through the vpn.
split-tunnel-policy tunnelspecified
split-tunnel-network-list value split-networks
!!! Only one simultaneous login is allowed.
vpn-simultaneous-logins 1
!!! No activity from the client within last 5 minutes, vpn will be terminated automatically.
vpn-idle-timeout 5
!!! Traffic through vpn will be subjected for inspection to a acl named anyvpn-filter.
vpn-filter value anyvpn-filter
!!! Define dns server and domain suffix for the vpn client.
dns-server value 8.8.8.8
default-domain value family.local
webvpn
anyconnect dpd-interval gateway 300
anyconnect dpd-interval client 300
!!! Setting mtu for anyconnect to avoid fragmentation
anyconnect mtu 1400
!!! When a user connects to the vpn adress from a web browser, it shows an option to download the vpn client.
anyconnect ask enable default anyconnect
!!! When a user disconnects from the vpn, the client remains installed.
anyconnect keep-installer installed
Now we will bind everything together with a tunnel group -
tunnel-group anyvpn-radius-tunnel-group type remote-access
tunnel-group anyvpn-radius-tunnel-group general-attributes
!!! Authentication will be performed against radius/nps server
authentication-server-group anyvpn-radius-server-group
!!! Binding the group policy
default-group-policy anyvpn-radius-group-policy
!!! Binding the IP Pool
address-pool anyvpn-pool
tunnel-group anyvpn-radius-tunnel-group webvpn-attributes
!!! Authentication will be done using username/password
authentication aaa
!!! We will use url to select different groups. If we want to connect as a local authenticated user we will below url as our vpn connection string.
group-url https://192.168.199.170/radius enable
!!! This local authenticated group has a alias named "anyvpn-local-users" which is showed when we use web browser.
group-alias anyvpn-radius-users enable
If someone wants to do certificate based authentication, then we need to change "aaa" to "certificate" in the setting below. We are not using certificate based authentication.
tunnel-group anyvpn-radius-tunnel-group webvpn-attributes
!!! Authentication will be done using certificate
authentication certificate
NPS Server Configuration
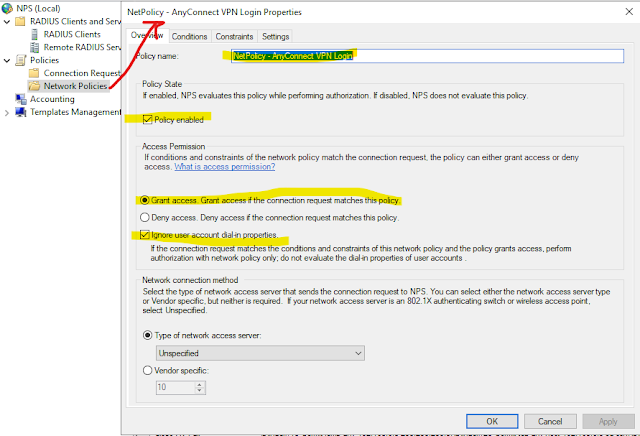
Now we will configure Windows NPS (Radius) server. We start by adding our Cisco ASA firewall as a radius client.
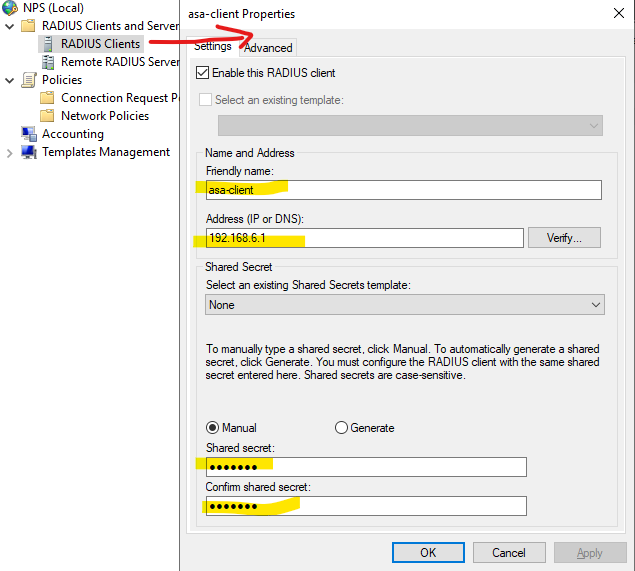 |
| 02 - Add ASA as a radius client Now we will define our policy which is straight forward, I am attaching pictures of how I have configured the policy - |
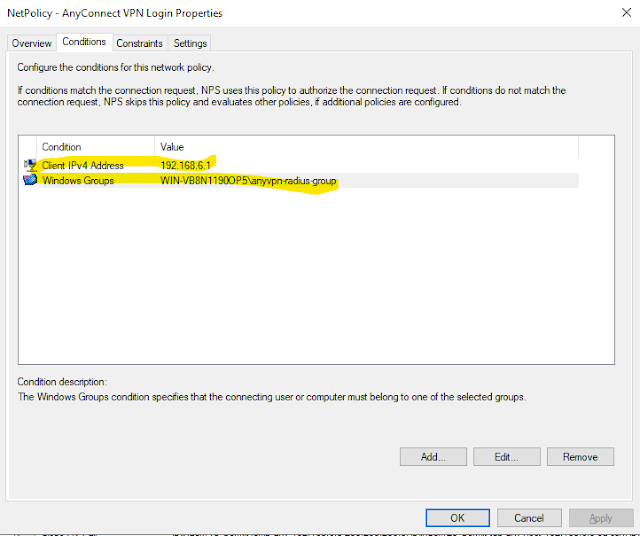 |
| 03-B - Network Policy For AnyConnect |
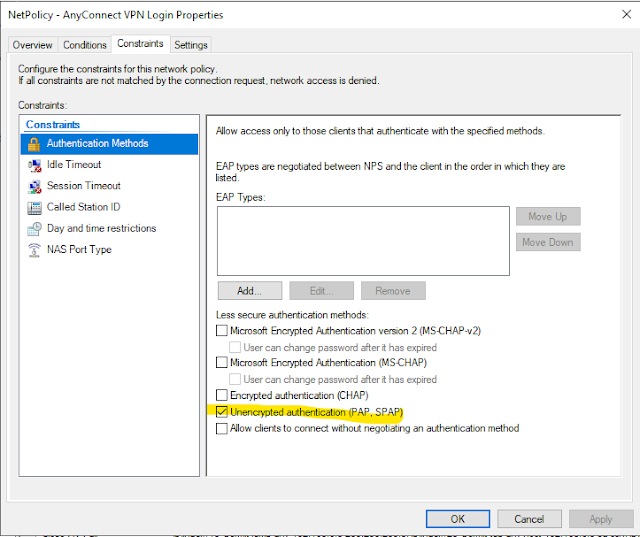 |
| 03-C - Network Policy For AnyConnect |
This time instead of using vpn-filter; we are using downloadable access-list from the radius server to define what network access a user has. In our previous blog post; we have used below access list. I am using strike-though to indicate that this acl is not configured in the ASA firewall; but will be configured in the radius server.
This time this access-list will be defined in the radius/nps server and upon successful authentication; this acl will be sent from the radius server to the anyconnect vpn client. And this is called downloadable acl from radius server.
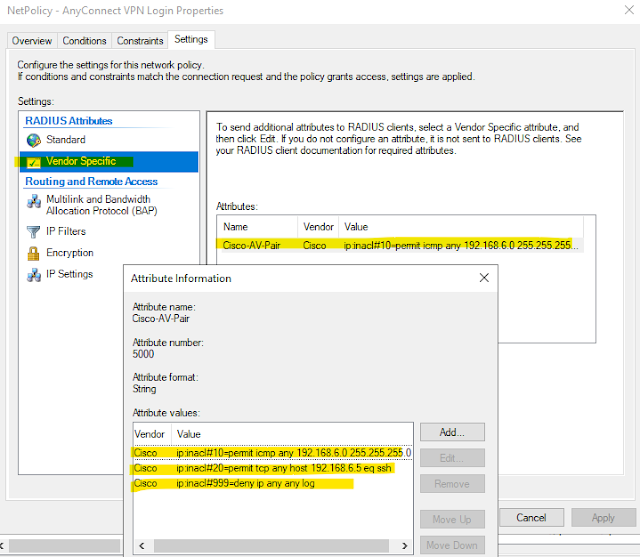 |
| 03-D - Network Policy For AnyConnect (Downloadable ACL) |
Verification
Now we will try to connect to the VPN through the anyconnect client -
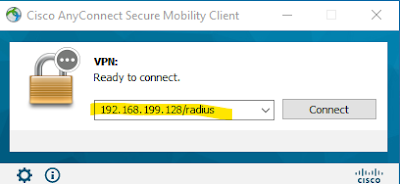 |
| 04 - AnyConnect login with vpn client |
Look at the connection string, it is same as the url defined in our tunnel group. After entering our credentials, we will be connected with the vpn.
Now we will have a look at the client's IP settings and routing table.
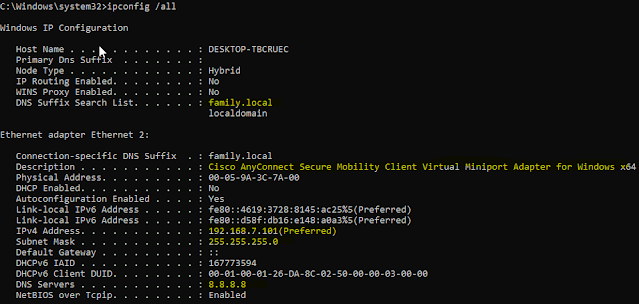 |
| 04 - AnyConnect client IP settings |
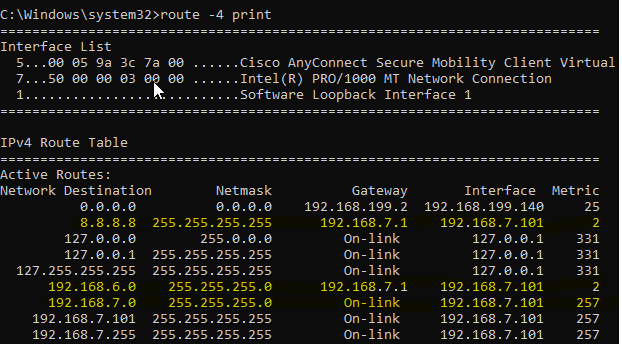
And the routing table -
We can see from the routing table that dns address (8.8.8.8/32) and ASA's inside network (192.168.6.0/24) is routed through the tunnel.
Now we will try to do ssh to the Debian-Client (192.168.6.5) and we can login successfully -
C:\Windows\system32>ssh root@192.168.6.5
root@192.168.6.5's password:
Linux deb10 4.19.0-10-amd64 #1 SMP Debian 4.19.132-1 (2020-07-24) x86_64
Now verify from the ASA -
Below command has long output, I am showing only the interested part -
# show vpn-sessiondb detail anyconnect
Session Type: AnyConnect Detailed
Username : testvpnradius Index : 18
Assigned IP : 192.168.7.101 Public IP : 192.168.199.140
Protocol : AnyConnect-Parent SSL-Tunnel DTLS-Tunnel
License : AnyConnect Premium
Encryption : AnyConnect-Parent: (1)none SSL-Tunnel: (1)AES-GCM-256 DTLS-Tunnel: (1)AES-GCM-256
Hashing : AnyConnect-Parent: (1)none SSL-Tunnel: (1)SHA384 DTLS-Tunnel: (1)SHA384
Group Policy : anyvpn-radius-group-policy
Tunnel Group : anyvpn-radius-tunnel-group
SSL-Tunnel:
Tunnel ID : 18.2
Assigned IP : 192.168.7.101 Public IP : 192.168.199.140
Encryption : AES-GCM-256 Hashing : SHA384
Ciphersuite : ECDHE-ECDSA-AES256-GCM-SHA384
Encapsulation: TLSv1.2 TCP Src Port : 52558
TCP Dst Port : 443 Auth Mode : userPassword
Idle Time Out: 5 Minutes Idle TO Left : 3 Minutes
Client OS : Windows
Client Type : SSL VPN Client
Client Ver : Cisco AnyConnect VPN Agent for Windows 4.9.01095
Filter Name : AAA-user-testvpnradius-9bf08b7
From above output we can see that, all the necessary settings are applied to client - group-policy, tunnel-group and dynamic filter from radius server.
Now we will look at this downloadable acl which was applied to the connected vpn user -
# show access-list AAA-user-testvpnradius-9bf08b7
access-list AAA-user-testvpnradius-9bf08b7; 3 elements; name hash: 0x3540ac43 (dynamic)
access-list AAA-user-testvpnradius-9bf08b7 line 1 extended permit icmp any4 192.168.6.0 255.255.255.0 (hitcnt=0) 0xfb00f16e
access-list AAA-user-testvpnradius-9bf08b7 line 2 extended permit tcp any4 host 192.168.6.5 eq ssh (hitcnt=0) 0x2ae6a86b
access-list AAA-user-testvpnradius-9bf08b7 line 3 extended deny ip any4 any4 log informational interval 300 (hitcnt=34) 0x21df03fa
That's about it - How to configure anyconnect vpn with with radius authentication and dynamic acl.

Comments
Post a Comment